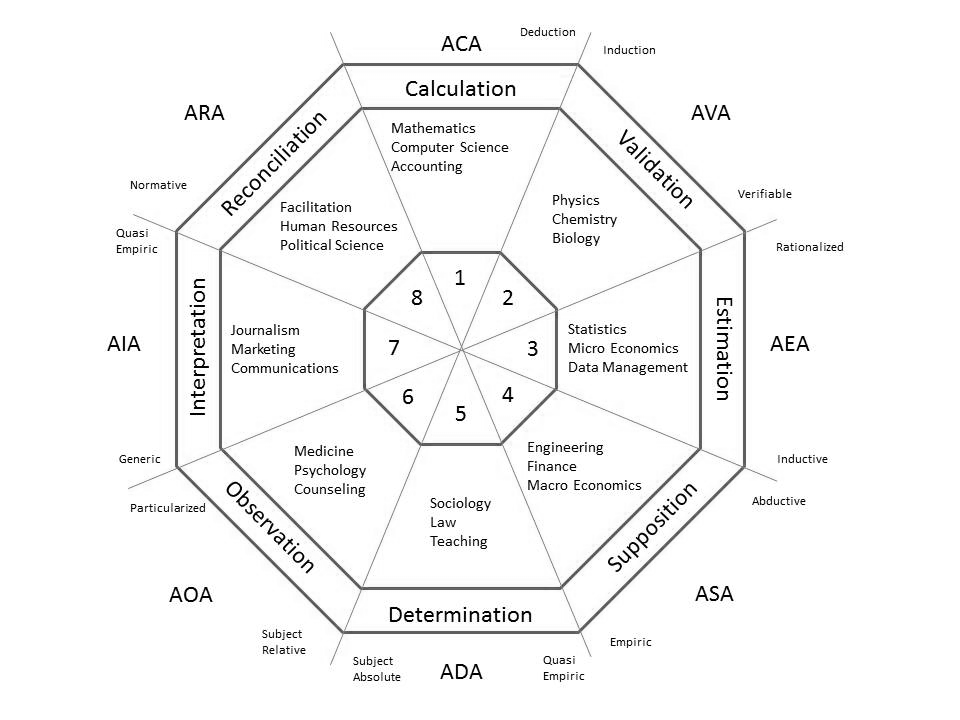
The analysis of analysis subject matter is very broad in scope. With the many combinations of parameters of interest, in order to gain traction for discussion, the Greenfields model provides a number of simplifying representations, allowing depth of study and yet coverage of the broader concerns. The taxonomy of the greenFields Model is as set out below.
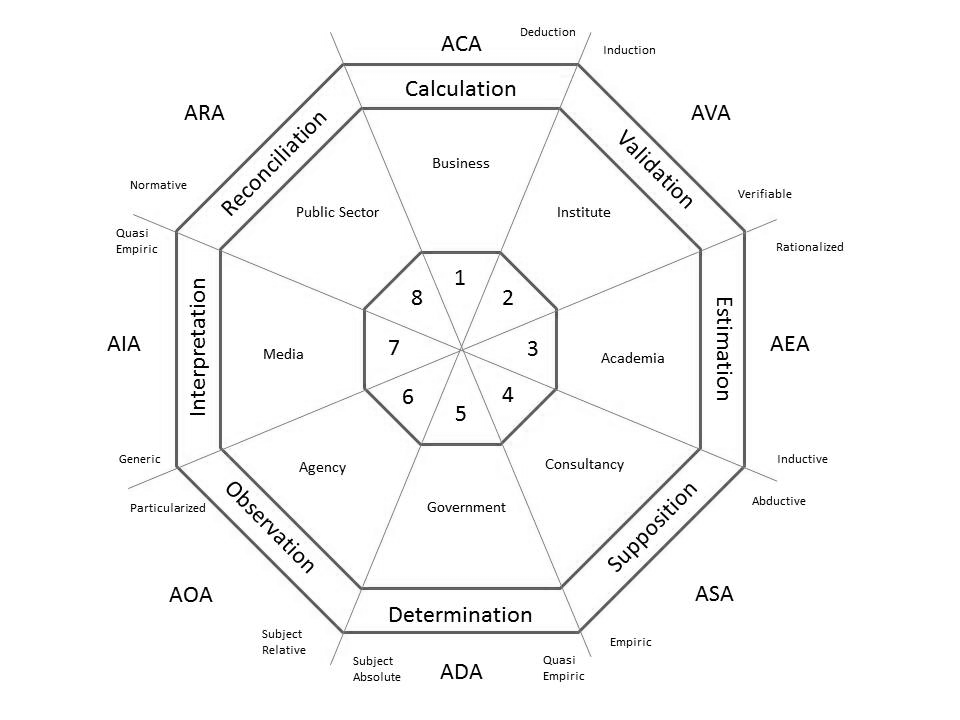
The greenFields Model taxonomy reduced analyses to three programs, each with an introductory context and each with eight modules of familiar practice. The Analysis of Analysis is initiated from first principles and is expanded to encompass analytic questions of key significance today. To build this context, three parties are proposed as the key participants in our view of analyses: “The Individual”, “The System” and the “Meta System”.
The three program perspectives are the individual, the system and the meta system.
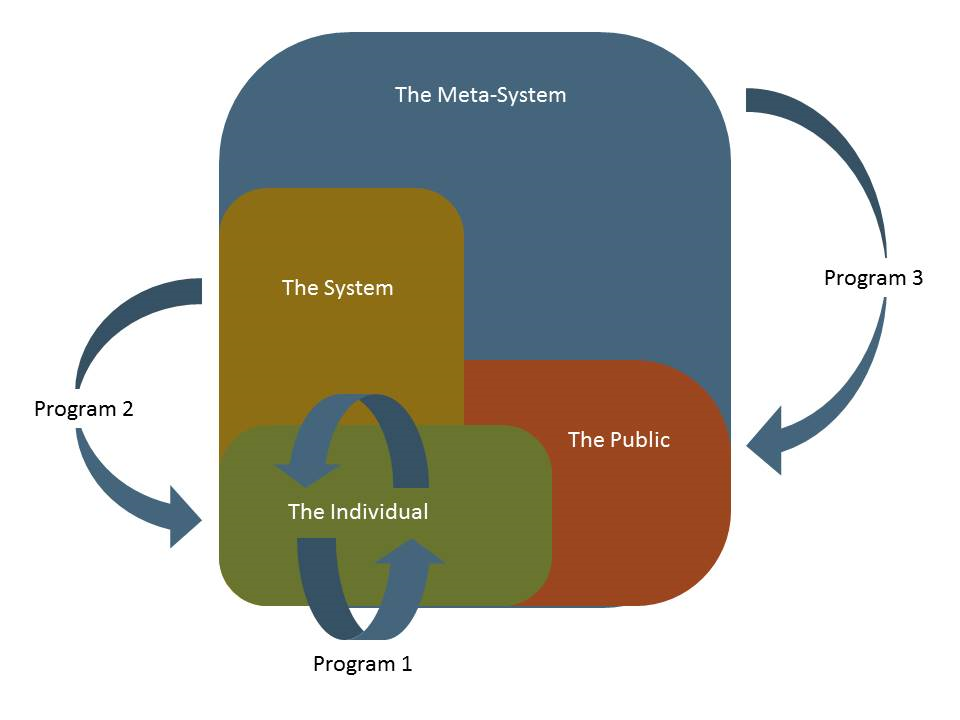
This perspective considers the “individual” analyst conducting analyses, confronting cognitive issues in implementation of scientific methodology. In this perspective, one could say integrity in analysis is internally determinate – just the analyst and the procedures. The focus is on the pluralism created by adherence to tactical procedure and the individual behaviours that determine integrity in these analyses.
This perspective considers the professional analyst working for or representing a corporate group or “system” which has larger objectives for the analysis beyond pure integrity in method. Here, the analyst is to balance needs of the profession with needs of the system. The focus is on the pluralism created by ethical responsibility to the profession and ethical responsibility to the system.
This perspective considers the world authorities providing society with analyses that further objectives of those authorities. In this perspective, “The meta system”, the analysis of analysis provides a basis for determine fact vs. fiction in analytic representations that are influencing world decisions. The focus in on the pluralism created by the various interests within the meta system and society’s propensity for interest and ability to separate fact from fiction.
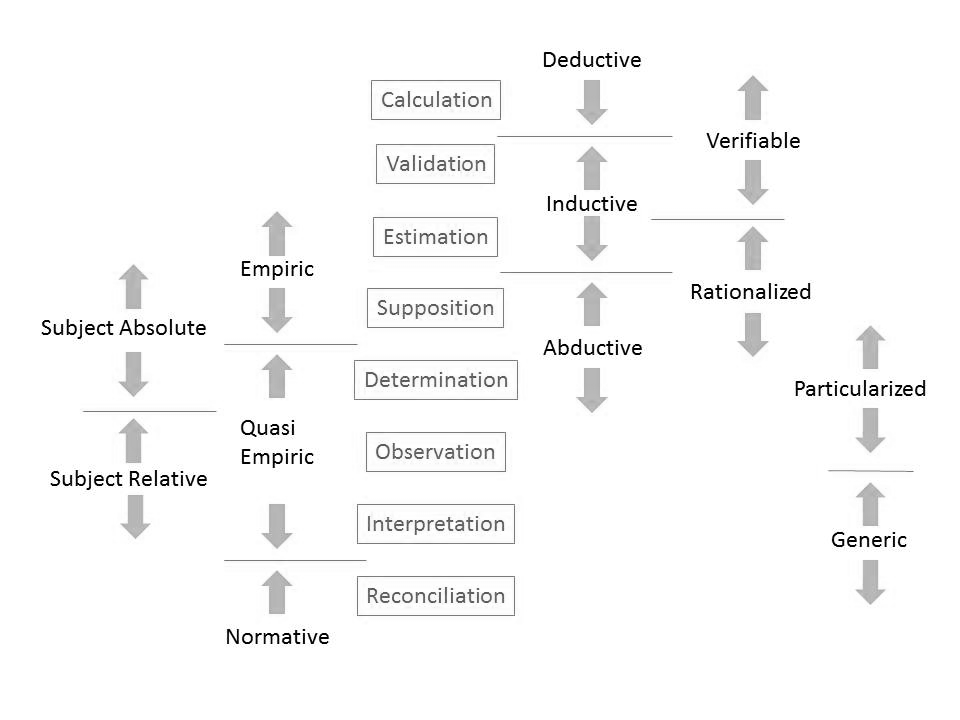
The analyses are established based on the “reasoning”, the “certainty”, the “rationality”, the “dependency” and the “entity” as follows:
Reasoning means: whether the analysis is deductive, inductive or abductive. Terminology here includes:
Conjecture in analysis is considered as either “verifiable” or “rationalized”.
Rationality in analysis is considered as either “empiric”, “quasi-empiric” or “normative”.
Dependency in analysis considers whether the subject of study is separate from, or joined with, the analysis.
Entity in analysis considers whether the analysis pertains to a particularized subject or is generic in nature.
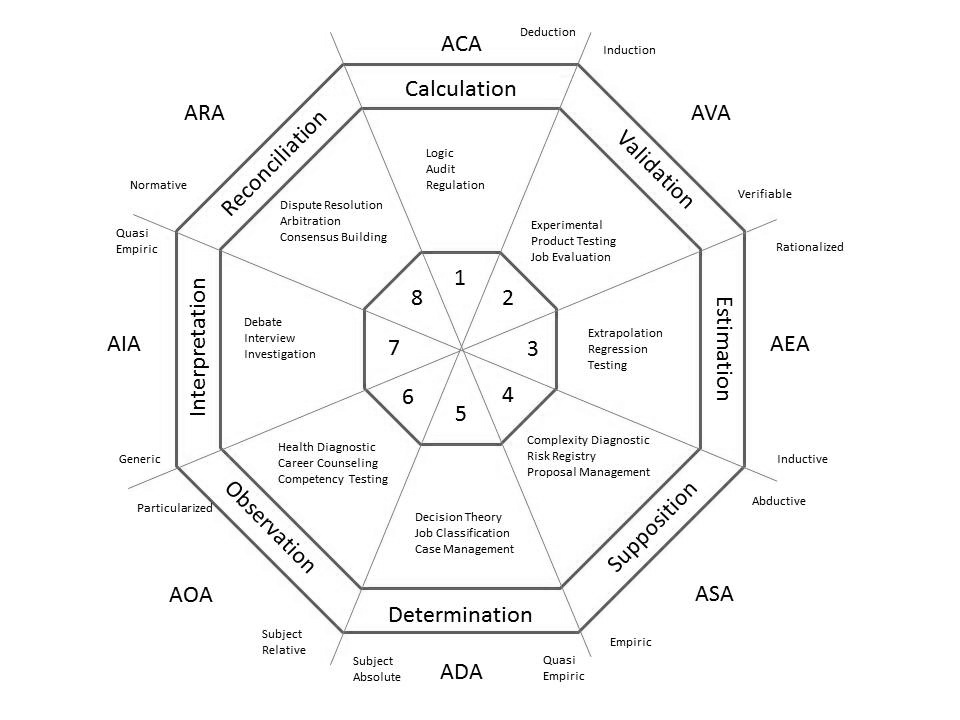
The foregoing distinctions define the eight archetypes that underpin each of the eight modules as illustrated in the following graphic.
In summary, the Modules are:
|
Reasoning |
Certainty |
Rationality |
Dependency |
Entity |
Example |
Archetype |
Module |
|---|---|---|---|---|---|---|---|
|
Deductive |
Verifiable |
Empiric |
Separate |
Particularized |
Accounting |
Calculation |
M1-ACA |
|
Inductive |
Verifiable |
Empiric |
Separate |
Particularized |
Science |
Validation |
M2-AVA |
|
Inductive |
Rationalized |
Empiric |
Separate |
Particularized |
Statistics |
Estimation |
M3-AEA |
|
Abductive |
Rationalized |
Empiric |
Separate |
Particularized |
Engineering |
Supposition |
M4-ASA |
|
Abductive |
Rationalized |
Quasi-empiric |
Separate |
Particularized |
Law |
Determination |
M5-ADA |
|
Abductive |
Rationalized |
Quasi-empiric |
Joined |
Particularized |
Medicine |
Observation |
M6-AOA |
|
Abductive |
Rationalized |
Quasi-empiric |
Joined |
Generic |
Journalism |
Interpretation |
M7-AIA |
|
Abductive |
Rationalized |
Normative |
Joined |
Generic |
Facilitation |
Reconciliation |
M8-ARA |
The modules of the greenFields model are defined by the combinations of the above parameters as detailed below.
ACA is a deductive, verifiable, empiric, several, particularized archetype. The ACA is an analytic archetype that establishes truth in a hypothesis through “deductive reasoning.”
AVA is an inductive, verifiable, empiric, several, particularized archetype. The AVA is an analytic archetype that establishes truth in a hypothesis through verifiable “inductive reasoning.”
AEA is an inductive, rationalized, empiric, several, particularized archetype. The AEA is an analytic archetype that establishes truth in a hypothesis through certainty that is approximate.
ASA is an abductive, rationalized, empiric, several, particularized archetype. The ASA is an analytic archetype that establishes truth in a hypothesis through abductive reasoning.
ADA is an abductive, rationalized, quasi-empiric, several, particularized archetype. The ADA is an analytic archetype that establishes truth in a hypothesis through the rationality of partial empiricism.
AOA is an abductive, rationalized, quasi-empiric, joined, particularized archetype. The AOA is an analytic archetype that establishes truth in a hypothesis that has a subject-relative dependency.
AIA is an abductive, rationalized, quasi-empiric, joined, generic archetype. The AIA is an analytic archetype that establishes truth in a hypothesis that is a group-based entity.
The ARA is an analytic archetype that establishes truth in a hypothesis that is normative. ARA is an abductive, rationalized, normative, separate, generic archetype.
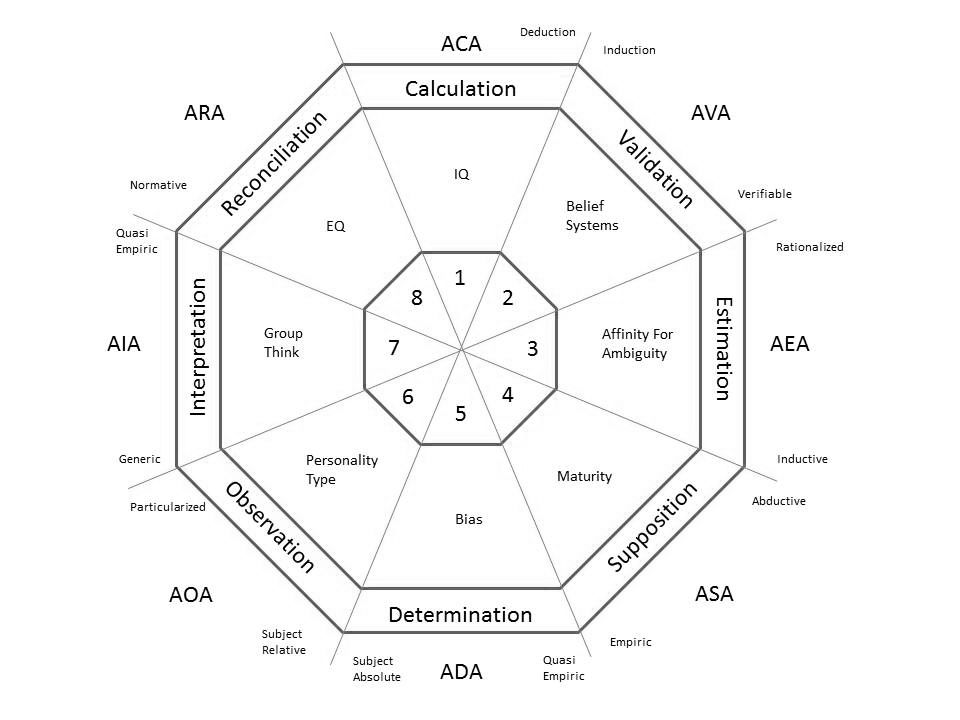
Within each of the Modules there are five sections: S1: The Approach to Analysis, S2: The Human Factors, S3: Analysis of Analysis, S4: Case Studies, and S5: References.
Program 1: Analytic Disciplines
Program 1: Assignment of Human Factors
Program 2: Analytic Disciplines
Program 2: Assignment of Human Factors
Program 3: Analytic Disciplines
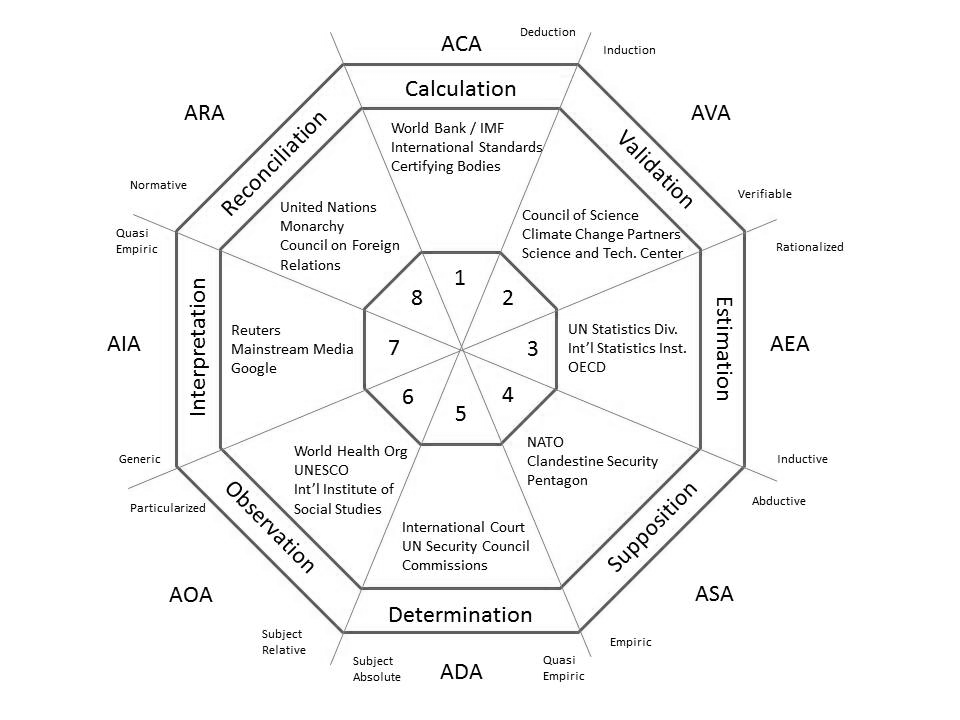
Program 3: Assignment of Human Factors
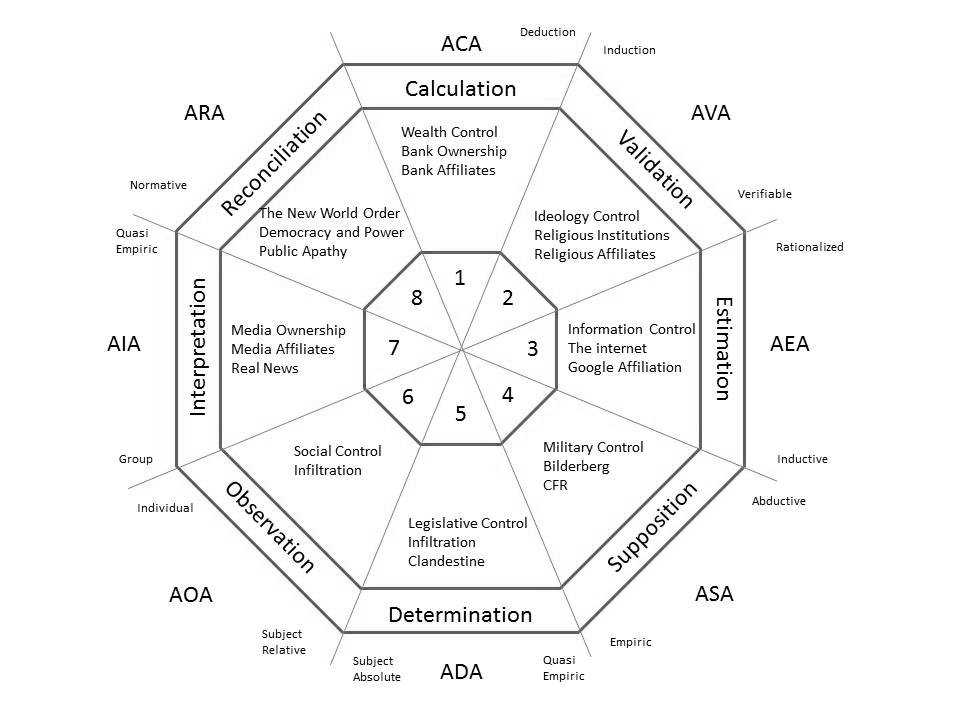
Whilst Program’s 1 and 2 are largely based on norms-in-practice - a “well trodden path” for society, Program 3 is a “mindscaping” that is less well established. Hence, expanded discussion is provided herein on how science-based analysis can be brought to bear in separating fact from fiction in the analytics relating to major conspiracy theories.
“Eternal vigilance is the price of liberty”
- Thomas Jefferson
Vigilance is a patriotic duty where one is fortunate enough to live in a democracy. It thus follows that keeping an open mind to the notion of conspiracy theories.
The various renditions of the truth surrounding world shaping events leads to intensive debate and often little in the way of conclusive agreement. Program 3 provides an analytic framework for assessing what are commonly referred to as “conspiracy theories.”
We know from our history that the forging of the international map has been through the clash between power structures competing for pre-eminence.
The conspiratorial thinking considers the world events as “a grand chess board” (ref. Zibigniew Brzezinski). Mr. Brzezinski has been a major architect for the New World Order and US foreign policy for many decades.
Without attributing fact to any of this, the top 15 conspiracies indicated by Liberty Voice (http://guardianlv.com/2014/03/the-worlds-top-15-conspiracy-theories-of-all-time/) are:
The assertion in conspiracy theories is that there is a difference between the official narrative, the “cover story”, and a backing reality. With this, the official story is thought to be part of the conspiracy, a narrative designed to engineer public opinion to favour an ulterior motive to those developing the official narrative. As part of the conspiracy theory is the allegation that the evidentiary record is susceptible to tampering and thus does not provide a sufficient basis for proving or disproving the theory.
The various hypotheses, the official story, the various conspiracy theories all appear to be well thought through by respected analysts and yet they often lead to differing conclusions.
In viewing geopolitics, the mainstream media tends to focus on the countries’ leaders, their personalities, as it to suggest that these people have control over the domestic and foreign policy of their nation. Together, through viewing editorial columns, interviews, talk shows, the notion that the character of the recognized leader bears out on foreign policy is reinforced in our minds.
If, in your analysis of geopolitics, you find yourself debating the character of the leadership, then you likely adhere to the first protocol and thereby, as a matter of adherence to societal orthodoxy, you won’t look beyond and thereby will not see beyond.
If this hypothesis is correct, then we and our mainstream media are on the right path.
There are many analysts that are recognized as being world renowned experts that simply live in the first protocol and reinforce their beliefs through intensive analysis of world events viewed only through the lens of the first protocol. Debate reduces to good guy – bad guy simplicity. Controversial world-shaping events are viewed as random acts.
If however, as those who subscribe to higher protocols suggest, there is a systemic external determinacy to countries’ domestic and foreign policy, the main stream media would be, not only off base, but distracting analytic thinking away from the true causation.
Further to the point held by the higher protocol-ers, the mainstream media is shaped by a number of influences. It must cater to the need of the general public for reasonable simplicity, it must remain within allocated time segments, it must pander to the business interests of its ownership and their commercial interests, it must maintain a tone of allegiance and patriotism etc. These non-analytic constraints on discussion pose a series of filters on reality. Unfettered by these filters, freedom of analysis on the internet (rightly or wrongly) provides a more open diversity of alternative realities for the analyst to consider.
For those limiting their perspective to the first protocol, they must rationalize how the major power wielding organizations on the plant never appear on the news – as if to consider them as either non-existent or of no consequence. Terminology suggested herein for Program 3 is largely off limits in mainstream debate.
World governance has always been a “forging” process by competing elements – democracy vs. hegemony by others. What makes us think the forging has finished?
Those advocating a systemic causation by these powerful groups hold the burden of proof according to the principles of Occam’s razor.
In an attempt to establish common analysis, AOAI suggests the following:
Sound analytic practice suggests erring on the side of open thinking and broad considerations. Sound analytics does entail subscribing to them. Sound analytics does entail not being afraid to look.
“Critical thinking is that mode of thinking - about any subject, content, or problem - in which the thinker improves the quality of his or her thinking by skillfully taking charge of the structures inherent in thinking and imposing intellectual standards upon them.”
- The Critical Thinking Community
In Statistical parlance, the official narrative is a “null hypothesis: - a statistical hypothesis to be tested and accepted or rejected in favor of an alternative; specifically: the hypothesis that an observed difference (as between the means of two samples) is due to chance alone and not due to a systematic cause” (ref. Websters).
A conspiracy theory is the alternative hypothesis, asserting a greater systemic pattern of cause and effect in world events
“Procedure for deciding if a null hypothesis should be accepted or rejected in favor of an alternate hypothesis. A statistic is computed from a survey or test result and is analyzed to determine if it falls within a preset acceptance region. If it does, the null hypothesis is accepted otherwise rejected.” (ref – Business Dictionary.com)
Review the official narrative in regard to science – i.e. establish whether the official hypothesis is consistent with science or contrary to science.
“Once you eliminate the impossible, whatever remains, no matter how improbable, must be the truth.”
- Sir Arthur Conan Doyle
Obviously a theory that is not consistent with science leaves you with the prospect of reinventing science to suit the hypothesis or leaving science where it is and looking past the hypothesis. Put simply, a theory that violates science cannot then invoke science as the rationale for its conclusions. For example, the official narrative in 9/11 demolition of Building 7 or the JFK assassination magic bullet theory both violate the basic principles of physics.
“Scientists announced today they have discovered a cure for apathy. However, they claim no one has shown the slightest interest in it.”
- George Carlin
By and large society appears to advocate the official story. This is a protocol to which the mainstream media adheres. Here, conspiracy is dismissed as either not existing or not relevant to world affairs.
Evidence is “all the means by which any alleged matter of fact, the truth of which is submitted to investigation, is established or disproved”. (ref. Blacks Law Dictionary). In this context, the means of analysis are truncated based on belief, contrary to science.
Direct evidence is the proof and testimony that directly go to an issue at hand. (ref. Black’s Law Dictionary). Hence, Protocol 1 limits inquiry to the direct evidence and does not appear to extend the analysis to circumstantial considerations.
For the alternative media, where there is no adherence to the mainstream media’s protocol, there is the prospect that the analyst may connect the dots to form a contrary narrative that is not the truth and again various perspectives in this more open thinking advance differing conclusions.
Given the conspiracy theorists’ assertions that the direct evidentiary record may have been compromised as part of the conspiracy, attempting to refute this point requires analyses based on indirect or circumstantial evidence.
Circumstantial is “evidence which inferentially proves the principal fact by establishing a condition of surrounding and limiting circumstances, whose existence is a premise from which the existence of the principal fact may be concluded by necessary laws of reasoning.” (ref. Black’s Law Dictionary).
As a matter of basic logic, one cannot use Protocol 1 arguments to prove or disprove perspectives beyond that protocol.
It is suggested that the behaviour of alternative media is also limited in its behavioural protocols depending on how large a conspiracy they advocate. Thus alternative media is available in a variety of perspectives based on the limitations of Protocols 2 through 4.
Similarly, arguments of a lower protocol cannot be used to disprove arguments of a higher protocol.
“Occam’s Razor, also called law of economy or law of parsimony, principle stated by the Scholastic philosopher William of Ockham (1285–1347/49) that pluralitas non est ponenda sine necessitate, “plurality should not be posited without necessity.” The principle gives precedence to simplicity: of two competing theories that full cover the situation, the simpler explanation of an entity is to be preferred. The principle is also expressed as “Entities are not to be multiplied beyond necessity.”” (ref. Encyclopedia Britannica)
Bayes’ theorem is an important when considering whether it is reasonable to assume events that appear to coordinate in achieving a patterned outcome are random or the product of a systemic causation.
Bayes’ theorem is “a theorem about conditional probabilities: the probability that an event A occurs given that another event B has already occurred is equal to the probability that the event B occurs given that A has already occurred multiplied by the probability of occurrence of event A and divided by the probability of occurrence of event B” (ref – Merriam Webster).
For example, the notion promoted in the Main-stream Media that the JFK assassination was by a lone gunman named Oswald and the RFK assassination was by a lone gunman named Sir Han Sir Han, while both contribute to ensuring the Kennedy’s are not in power.
As further events are added to a pattern that support the hypothesis that external powers are conspiring to ensure Kennedy’s are not in the White House, reasonable in the conjecture that these are random acts diminishes exponentially. Though applying Bayesian logic here does not prove the point, it provided a fair guide for the question, is it reasonable to pursue the conspiracy theory? As a further example on the Kennedy theme, there is conjecture by some that Chappaquiddick the death of John Kennedy Junior are potentially further acts accepted by the mainstream media as being random that contribute to a pattern supporting the conspiratorial hypothesis. This does not prove conspiracy but it would appear to be analytically prudent to raise the question and test the hypothesis.
Protocol refers to the self-imposed limits of societal inquiry. The tendency for members of society to draw boundaries around inquiry – to artificially set a ceiling based on comfort and feelings of faith, allegiance or respect. For those setting the boundaries, this is a patriotic duty where others thinking outside this box are shunned as heretics or “conspiracy theorists”. “System justification theory (SJT) is a scientific theory within social psychology that proposes people have a motivation to defend and bolster the status quo, that is, to see it as good, legitimate, and desirable.
According to system justification theory, people not only want to hold favorable attitudes about themselves (ego-justification) and their own groups (group-justification), but they also want to hold favorable attitudes about the overarching social order (system-justification). A consequence of this tendency is that existing social, economic, and political arrangements tend to be preferred, and alternatives to the status quo are disparaged.
Satisfies three distinct human needs:
(ref - e-Study Guide for: Social Psychology by Saul Kassin),
“Groupthink occurs when individuals in a group fail to express their doubts about the group's dynamic, direction or decisions because of a desire to maintain consensus or conformity. Thus the group may be on a headlong rush to error or disaster and no-one speaks up because they don't want to rock the boat.”
(ref. Rational Wiki)
The alleged source of the conspiracy varies with analyses conducted. However, it is suggested they can be grouped into four general categories of speculation.
Protocol 1 asserts that officials are free thinking and exercise their conscience in conducting themselves. Here, the official narrative is deemed to be correct. Faith precludes scientific inquiry beyond this horizon.
Protocol 2 asserts a conspiracy by “big business” entities that have unduly infiltrated official office and have implemented the official narrative as a cover to engineer public opinion.
Protocol 3 asserts a higher level conspiracy by elite families and world bankers that have implemented the official narrative as a cover to engineer public opinion. Faith precludes scientific inquiry beyond the “big business” perspective.
Protocol 4 asserts the highest level conspiracy, by the international guilds – major religious organizations and their affiliated secret societies that are implementing the New World Order and have implemented the official narrative as a cover to engineer public opinion.
These categories of perspective are protected by the analyst as they are heavily vested in the belief system – as if to suggest alternative perspectives are an affront to their belief system and are therefore too disturbing. Here, analysts will be inclined to protect their perspective whether or not it is analytically sound. The very term “conspiracy theorist” is often used as a weapon of ridicule, suggesting the advocate of a conspiracy hypothesis, merely by thinking outside the box, is not of sound mind, is unpatriotic, is breaking with the group’s tradition and is thereby heretical.
Without declaring such a theory as valid or not, Program 3 provides an analytic framework for assessing whether review of direct evidence is warranted beyond the limits of the official narrative.
For Program 3, the greenFields model follows the procedure:
Where there is a high Bayesian correlation, society has a reasonable science-based expectation for inquiry further into direct evidence to seek substantiation for the official story.
Where there is low Bayesian correlation, the burden of proof is left with the theorist.
Through expanded input from interested analytic practitioners, it is hoped that the material herein can be improved and adapted toward establishing an Institute – “The Analysis of Analysis Institute”. As such, this website is merely a door opener to the subject matter.
Program 1 provides students and analytic practitioners with the cross section of procedural due diligence that has been honed through time for the various analytic disciplines. It provides a forum for cross pollinating amongst the eight modules selected coupled with the natural human tendencies in analysis – i.e. behaviours innate to humans that may contribute to less-than-objective analytics.
Program 2 provides an awareness that corporate objectives, by nature, may conflict with the fundamental of ethical standards. The very reason ethics is established through professional institutions is in recognition of this natural behaviour. Students and analytic professionals can review the broad cross section of professional codes and various system environments that are common place in society and that may contribute to less than professional analytics.
Program 3 provides an awareness of competing theories on international affairs, once that focuses attention on scientific inquiry over the current limitations of behavioural expectations (protocols). Students and interested members of society can review the breadth of the eight modules to discern patterns in power structure advancement, benefit accumulation (e.g. wealth) and interests that compete with the democracy we feel we have.
The learning objectives are as set out in the table below.
| Intro to Program 1 | Intro to Program 2 | Intro to Program 3 |
|---|---|---|
| Learning Objective: At the completion of P1 participants will be able to identify generally accepted procedures for integrity in analysis and will gain sensitivity to the personal behaviours that challenge this objectivity. |
Learning Objective: At the completion of P2 participants will be able to identify the ethics of integrity in analysis and will gain sensitivity to the corporate pressures that challenge this integrity. |
Learning Objective: At the completion of P3 participants will be able to identify sources of globally-based analyses that are part of a larger agenda. |
| Baseline Reference -Truth -Meaning -Rationality -Objectivity |
Baseline Reference -Duty to Profession -The Professional Analyst -Duty to Society -Duty to Stakeholders |
Baseline Reference -Global Power Brokers -Principles of Operation -Societal acceptance |
| Pluralism: Objective Analysis and The Individual Within |
Pluralism: Ethical Analysis and System Thinking |
Pluralism: Moral Analysis and Meta-system Gaming |
A certification program could be considered – certification to Program 1, 2 or 3. Successful candidates would be granted the status (for example) “Analytic Professional”.